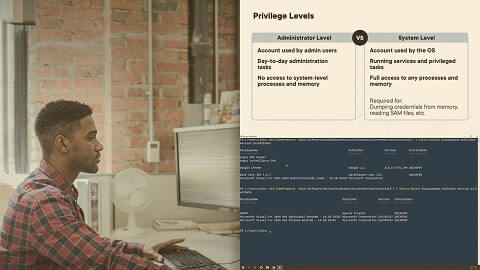
In a red team engagement, after getting initial access to your target environment, you need to escalate your privileges, establish persistence and execute your goals. As your objective is to stay stealthy, the best option is to leverage Windows native features, such as PowerShell, to conduct your post-exploitation activities. In this course, Post-Exploitation with PowerShell, you’ll learn how to execute all your post-exploitation activities using only Windows native commands. First, you’ll explore how to escalate your privileges in the compromised system. Next, you’ll discover how to create persistence so you can access the system at any time. Finally, you’ll learn how to collect and exfiltrate sensitive data. When you’re finished with this course, you’ll have the skills and knowledge of PowerShell needed to perform post-exploitation on a red team.
HOMEPAGE – https://www.pluralsight.com/courses/powershell-post-exploitation
Free Download Link-
Note: Comment below if you find the download link dead.


0 Comments