Security , Shop
OFFENSIVE MOBILE REVERSING AND EXPLOITATION
This is a completely hands-on course designed for beginners and intermediate students. Instead of just slides, attendees will get a chance to exploit all of the vulnerabilities taught by the instructors.
HOMEPAGE – https://sectrain.hitb.org/courses/offensive-mobile-reversing-and-exploitation-hitb2023ams/
Original Price: $4,299
Our Price: $25
Programming , Shop
AssetMapper: Modern JS with Zero Build System
Ever wanted to just… write modern JavaScript and have it work without needing to fuss with a build system?
Me too! And finally – thanks to advances in the web, web servers & new component from Symfony, it’s possible!
HOMEPAGE – https://symfonycasts.com/screencast/asset-mapper
Original Price: $25
Our Price: $5
Security , Shop
Certified Ethical Hacker Elite
You will understand how to use open-source intelligence to your advantage. Further, you will discover how to analyze and interpret network protocols and leverage Wireshark. Moving ahead, you will learn how to perform ethical hacking using Nmap. You will also learn how to perform information gathering and enumeration of Windows-specific services with Nmap and OpenVAS. You will then understand how …
Security , Shop
Offensive Development Training Course
White Knight Labs proudly presents “Offensive Development,” an intermediate-level course meticulously crafted for cybersecurity professionals. This program is not for beginners; it’s tailored for those looking to elevate their skills in the complex art of offensive cybersecurity.
HOMEPAGE – https://training.whiteknightlabs.com/offensive-development-training/
Original Price: $1,100
Our Price: $20
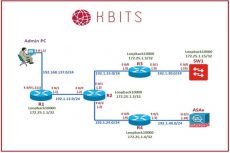
Networking , Shop
Khawar Butt – ACI
Khawar Butt offers detailed coverage of Cisco’s ACI Technology, its components and implementations. The course covers concepts like Fabric Discovery, Access Provisioning, Tenant Provisioning, End-Point-Groups (EPGs), Contracts, External Domains (L2OUT & L3OUT), Multi-Tenancy, MultiPod & Multisite. The course will also introduce Automation Scripting using POSTMAN. The course assumes no prior knowledge of ACI.
HOMEPAGE – https://kbits.live/courses/aci
Original Price: $1000
Our Price: $15
Programming , Shop
Flutter & Firebase Masterclass ( Complete Package )
Learn about Firebase Auth, Cloud Firestore, Cloud Functions, Stripe payments, and much more by building a full-stack eCommerce app with Flutter & Firebase.
HOMEPAGE – https://codewithandrea.com/courses/flutter-firebase-masterclass/
Original Price: $149
Our Price: $15
Programming , Shop
CSS Grid & Flexbox, v3
Explore CSS layouts in-depth, including Grid and Subgrid, Flexbox, responsive image techniques, media queries, and container queries. Learn how to apply these techniques to your next website, even if you haven’t worked with CSS layouts before.
HOMEPAGE – https://frontendmasters.com/workshops/css-grid-flexbox-v3/
Original Price: $39
Our Price: $5
Security , Shop
Malware On Steroids
The Malware On Steroids is the first course which is dedicated to building your own C2 Infrastructure and Payload. There are a lot of courses which focus on exploitation, reversing and other offensive stuff, but none of them focus on how you can build your own Command & Control Infra. This course focuses on a brief introduction towards Windows Internals …
Programming , Shop
LET’S GET CODING: Full Stack Developer Course
In this course, I will teach you how to code completely from scratch! You do not need to be a math whizz to code. Just have the urge to learn!
HOMEPAGE – https://www.codewithania.com/
Original Price: $499
Our Price: $20
Shop
Showing 1–9 of 1048 results