FortyNorth – Intrusion Operations 2021
₹1,250.00
Intrusion operations is our advanced Red Team training course. Modern day attackers are relentlessly developing new tradecraft and methodologies that allow them to successfully compromise hardened targets for a variety of motivations. While it may look easy from the outside, there are many latent steps that attackers take to ensure their success. Our job as red teamers is emulate this attack life cycle in an effort to identify and remedy these vulnerabilities.
This is our premier, advanced red teaming course. We’ve previously taught this content at BlackHat, BSides and 44Con. This course is recommended for intermediate level students.
Attackers bring unique perspectives, tools, and resources to the table in their efforts to accomplish their goals, requiring organizations to do the same by consistently applying new defensive technologies and procedures to prevent their environment from being breached. When conducting a red team assessment against organizations with mature security programs, you need to ensure you are using the latest tradecraft and techniques to help avoid detection. That’s where we come in!
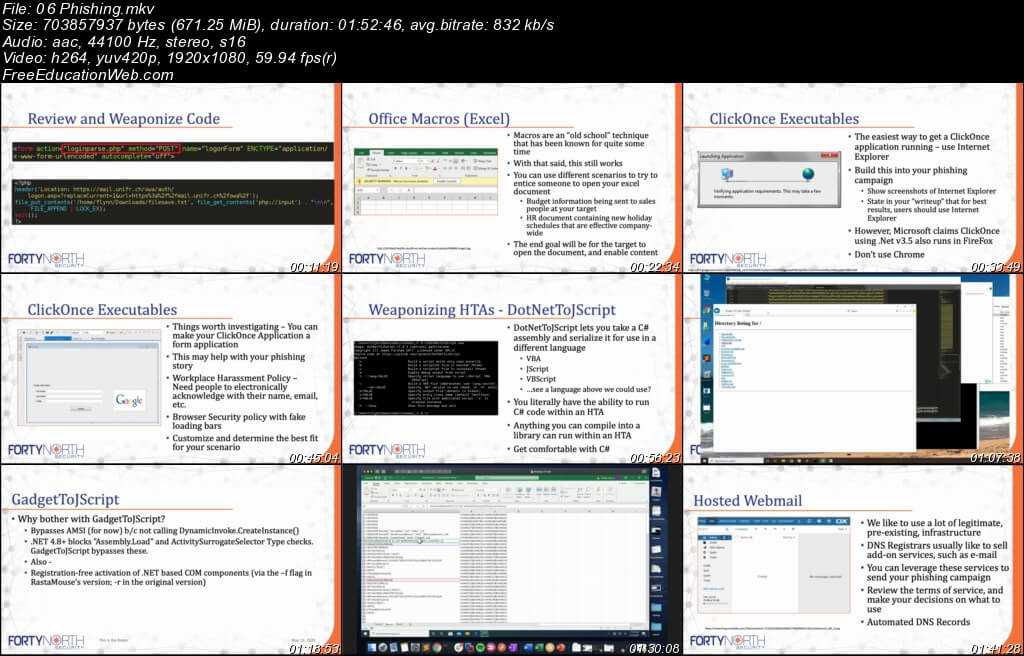
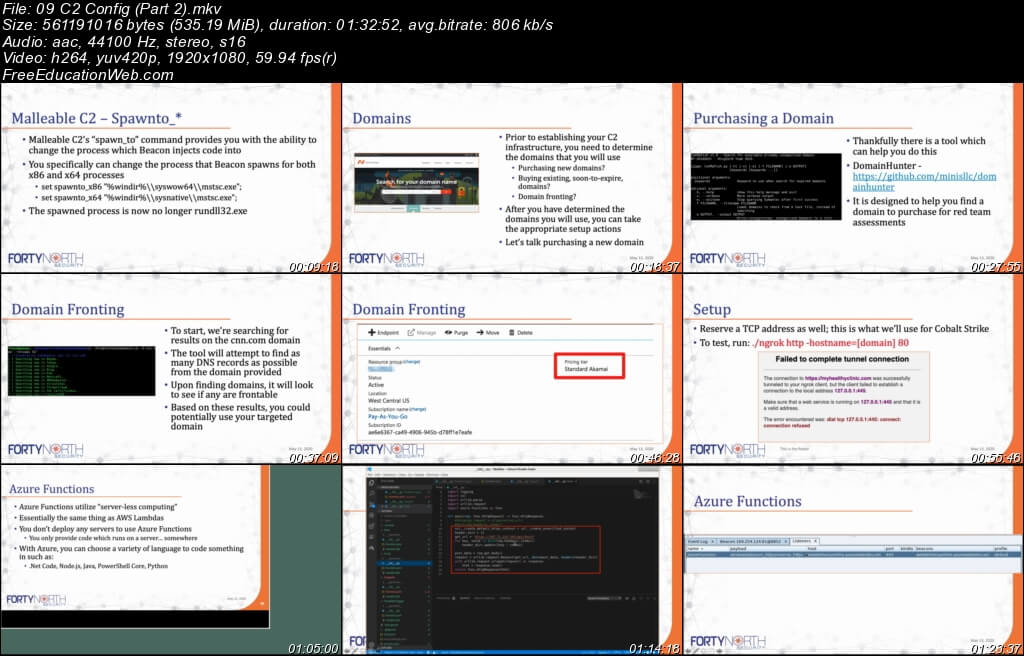
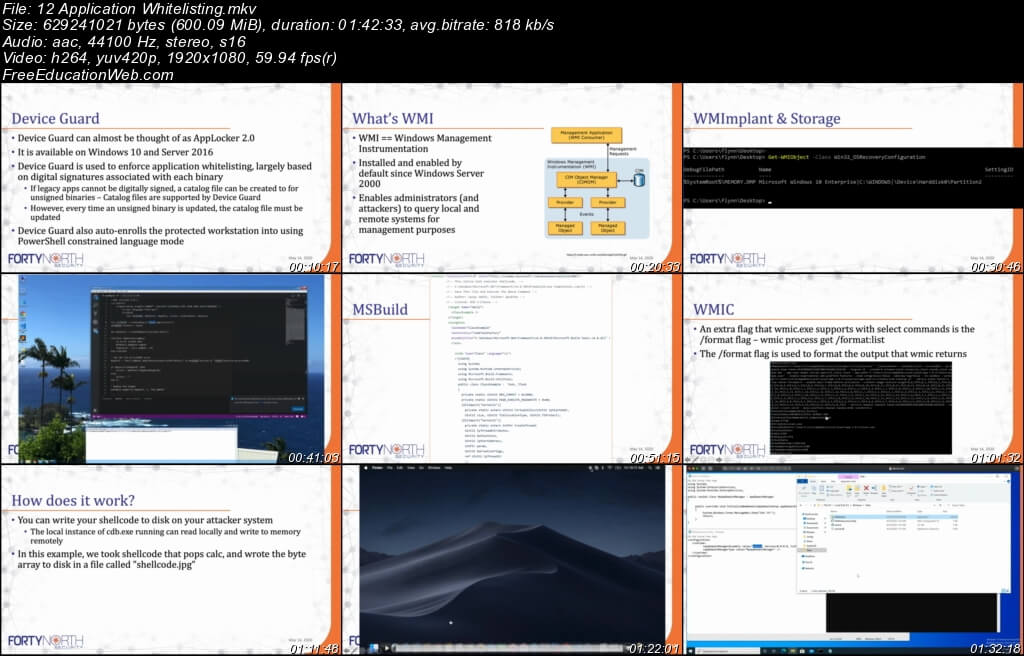
Step by step, we will take you through the attacker lifecycle and capture best practices that you can follow to protect your foothold within your target. You will start with no information, build a profile on your target, establish a foothold, persist within their environment, bypass modern defenses, and achieve the goals of your test. We will immerse students in an environment based on real-world defenses and require the application of techniques taught throughout the class. You’re going to learn methods to capture information about your target before even gaining access, write custom malware to evade detection, execute the latest application whitelisting bypasses to compromise protected systems, develop strategies for persisting within the target environment, and accomplish the goals of your assessment.
Original Price: $4000
Our Price: $15