Description
Size: 5.42 GB
Practical Threat Hunting includes:
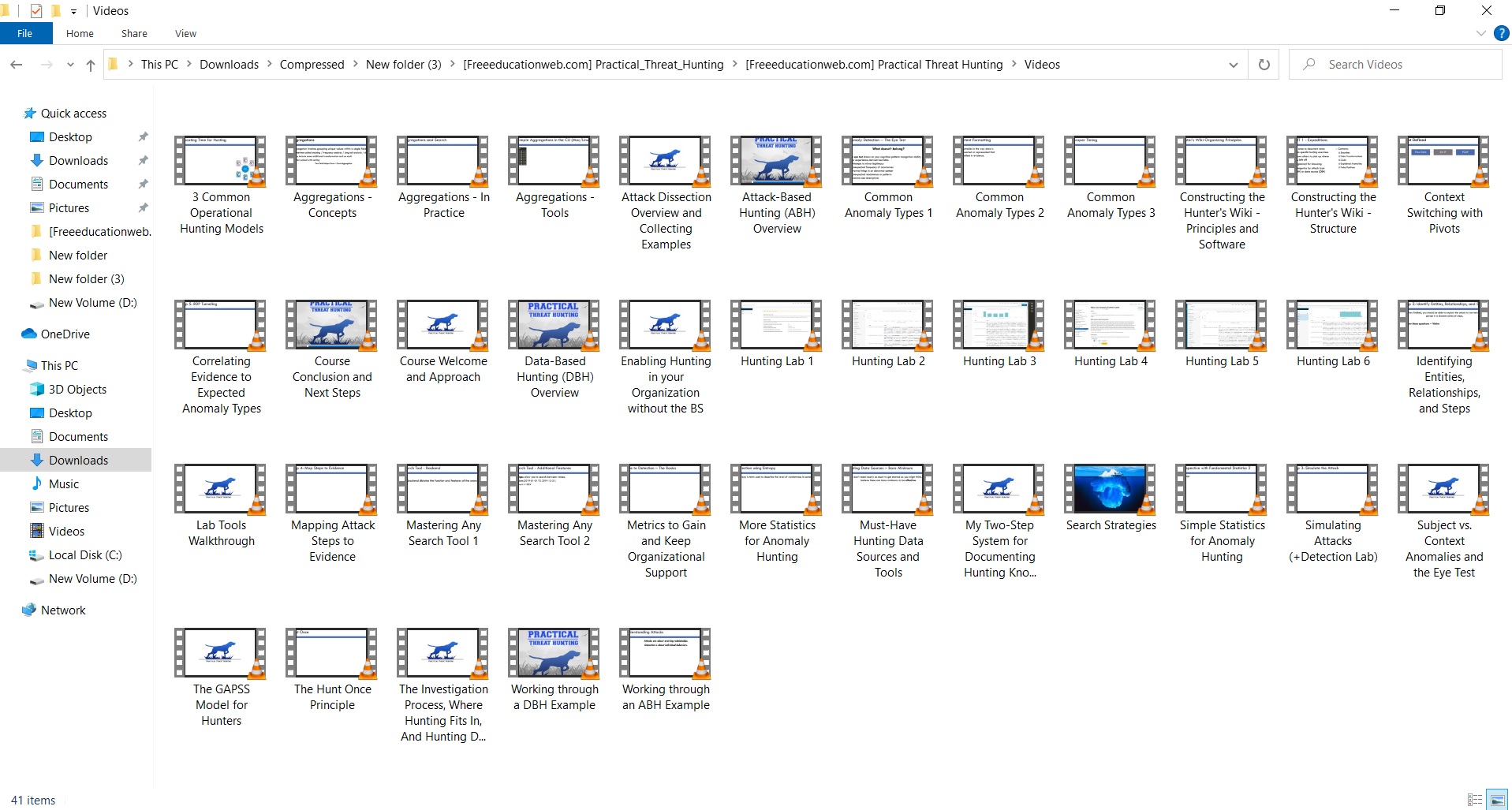
- Over 15 hours of demonstration videos. These videos will break down the concepts and skills you need to become an effective threat hunter.
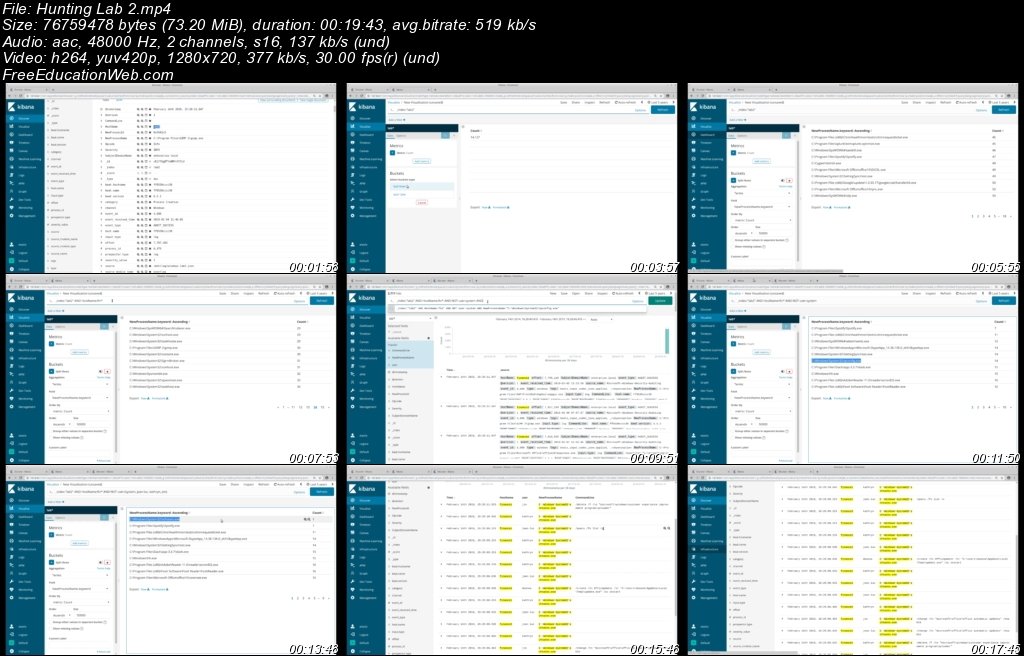
- Hands-on labs to help you develop and test your skills. You’ll complete hunting labs using an ELK-based virtual machine we’ve loaded with log data representing several real-world scenarios. Not familiar with ELK? Don’t worry, I’ve provided a short primer video to get you started and you can also watch videos of me working through the labs. I’ve also provided all the raw log data so you can work with it on the command line, or import it into your analysis tool of choice.
- Access to My Hunting Vault. I’ve compiled all the hunting expeditions mentioned in the course (along with several others) into PDF files you can use to reference as you’re hunting in your network. I’ve also included a wealth of additional information in PDF form, including a curated list of my favorite threat hunting tools and Twitter follows for hunting inspiration.
- Membership in our exclusive students-only learning community. In our discourse-powered forum, you can ask questions, share hunting strategies, view community investigation playbooks, participate in our virtual reading group, learn about upcoming courses, network with other students, and communicate directly with AND course authors. I also post short blog entries here that don’t appear on my public blog.
- Participation in our student charitable profit sharing program. A few times a year we designate a portion of our proceeds for charitable causes. AND students get to take part in nominating charities that are important to them to receive these donations.
You’ll learn:
- Two hunting frameworks: Attack-Based Hunting (ABH) and Data-Based Hunting (DBH)
- Techniques for leveraging threat intelligence and the MITRE ATT&CK framework for hunting input
- The 9 most common types of anomalies you’ll encounter when reviewing evidence.
- The 4 ways threat hunters most commonly transform data to spot anomalies
- Typical staffing models for hunting capabilities in organizations of all sizes along with pros/cons
- 5 metrics that support and enable threat hunting operations
- My two-step system for effective note taking while hunting (and how to transition those notes to longer-term storage for easy searching)
- An ideal design for a hunter’s wiki/knowledgebase
- A 5-step framework for dissecting and simulating attacks to prepare for hunting expeditions
You’ll also receive:
- A list of my favorite hunting data sources and tools
- A curated list of hunting expeditions to get you started
- A list of my favorite Twitter follows for daily threat hunting input
Practical Threat Hunting will teach you how to become an effective threat hunter regardless of the toolset by focusing on the habits and techniques used by experts.