Description
Size: 6.04 GB
Learn How To:
- Survey cybersecurity vulnerabilities
- Decipher Encryption and Hashing Algorithms
- Analyze Computer Incident Response Teams (CSIRTs) and Product Security Incident Response Teams (PSIRTs)
- Apply VERIS
- Perform DNS Analysis and Web Log Analysis
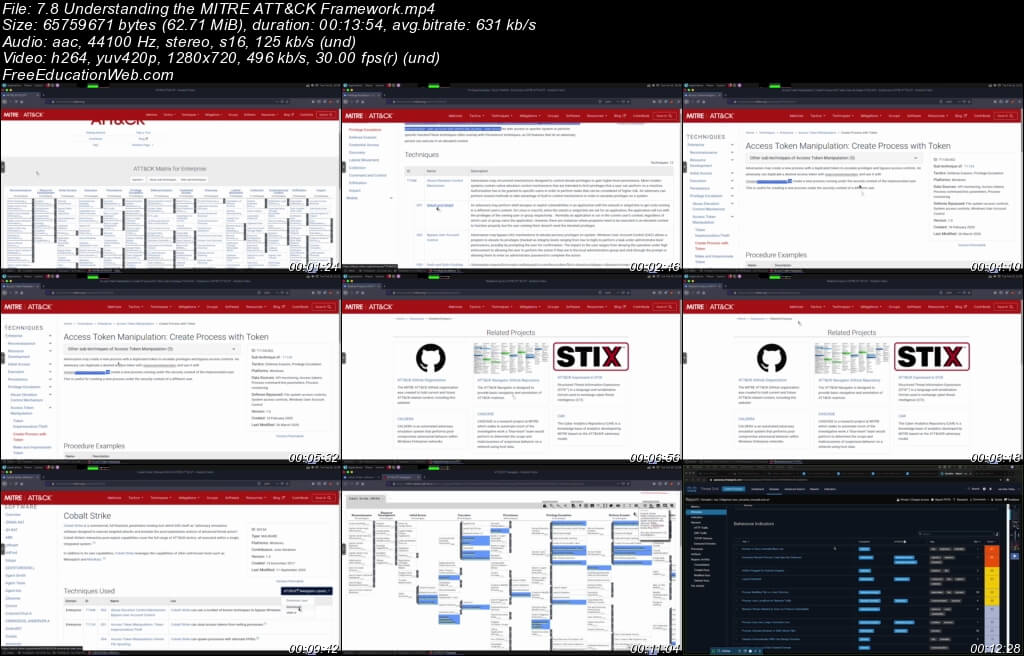
- Identify MITRE ATT&CK Framework
- Examine Asset and Threat Actor Attribution
- Examine Host-based Intrusion Detection
- Analyze Security Device Data
- Survey the TACACS+ Protocol
- Survey Open Source SDN Solutions
- Scope a Penetration Testing Engagement Properly
- Perform Footprinting through Social Engineering
- Scan beyond IDS and Firewall
- Survey Web Server Attack Tools
- Explore SQL Injection Tools
- Hack Bluetooth
- Build your own lab
- Create a Fuzzing Strategy
- Crack Passwords
- Hack iOS and Android OS
- Hack Android devices