Description
Size: 14.6 GB
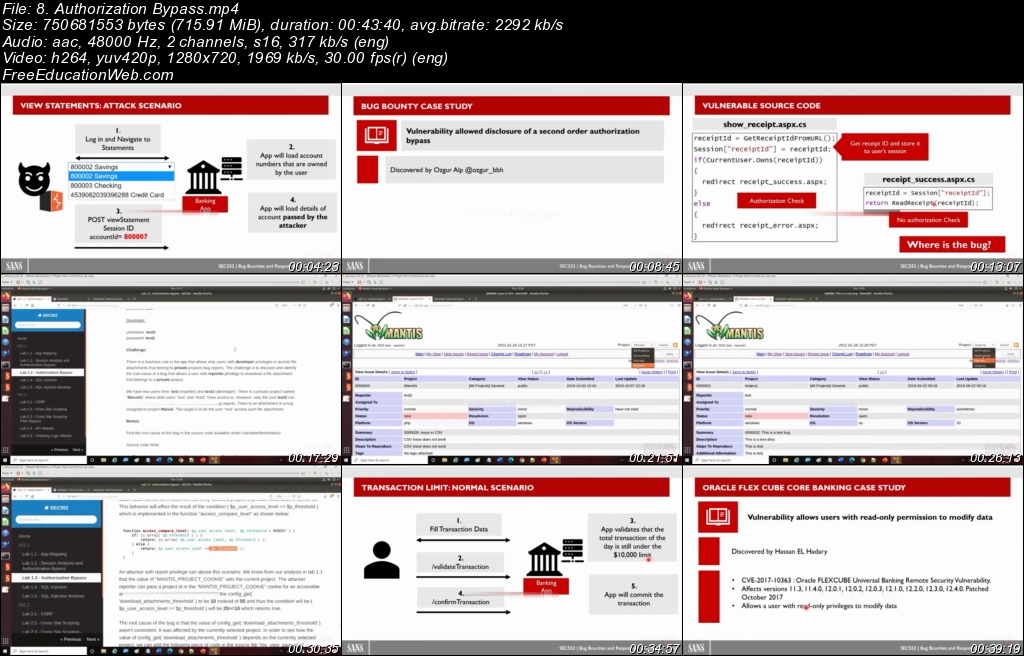
SEC552 is inspired from case studies found in various bug bounty programs, drawing on recent real-life examples of web and mobile app attacks. The experiences of different researchers yield ideas for pen testers and developers about unconventional attack techniques and mindsets. Each section of the course is influenced by bug bounty stories that are examined through the following structure:
- Attack concept: The idea, concept, and root cause of the attack.
- Test technique: How to test and discover the application security flaw manually and automatically.
- Attack exercise: This lab uses tools such as Burp Professional to analyze the vulnerable applications.
- Related bug bounty case study: Analysis of several bug bounty stories that are related to the attack.
- Defense techniques: The best security practices to defend from the attack and mitigate the application security flaws.
Who Should Attend SEC552?
- Penetration testers: The course will enrich the skills of pen testers through real-life stories and practical labs covering the most popular web and mobile app attacks.
- Software developers and architects: The course will help developers link attack and defense techniques while discovering security bugs in the source code before making the app public.
- Security engineers: The course will help attendees who are managing a bug bounty program or planning to implement one by enabling them to practice the techniques used by security researchers to report security bugs, and to verify if the bugs are valid or false positives.
- Network/system engineers: The course will help attendees fill the gap of application security and get started in the field.