Osquery for Security Analysis
₹415.00
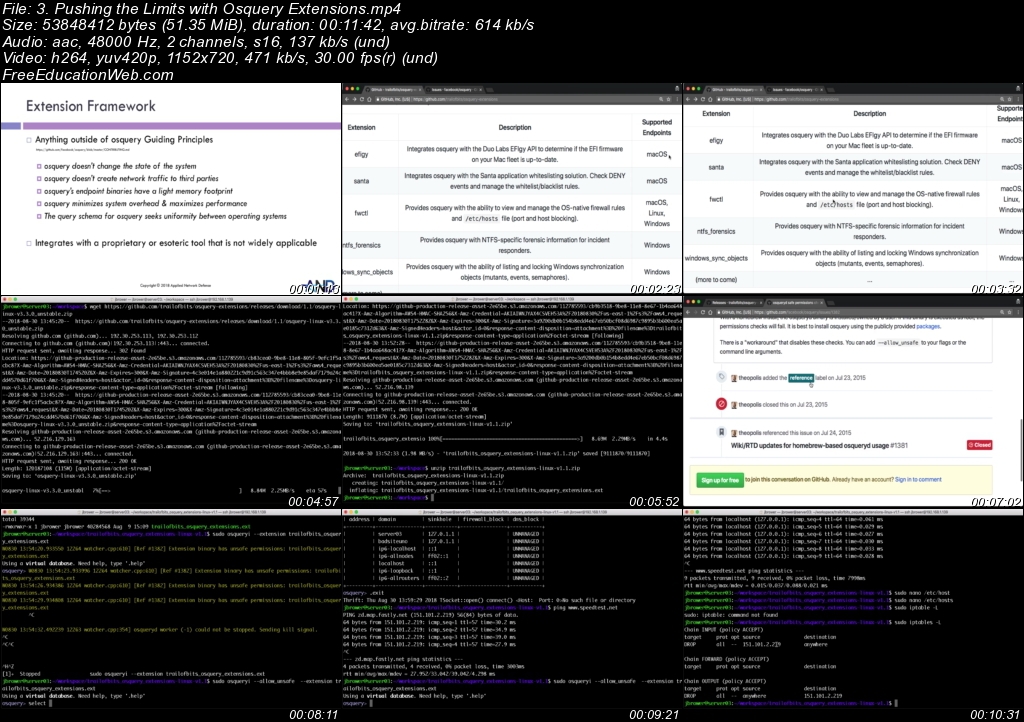
Osquery for Security Analysis will teach you how to use Osquery to perform thorough investigations of hosts on your network. This isn’t just an Osquery tutorial, it’s a course designed to help you improve your host-based investigation skills using one of the best tools for the job.
A production server that doesn’t normally communicate over the internet is exhibiting suspicious characteristics. It’s sending out weird bursts of network traffic to an external host you don’t know anything about. The traffic is encrypted, so network data won’t be helpful. You have to rely exclusively on host-based evidence to figure out what’s happening.
Now be completely honest with yourself. Would you be able to come to a conclusion about whether an attack has occurred? Would you be able to do it quickly? Would you be 100% certain about your determination?
If you answered no to any of those, then you aren’t alone. The truth is, investigating things on the host is overwhelming. There are so many places to look: the registry, prefetch, disk artifacts, operating system logs…the list goes on.
The problem isn’t just the number of rabbit holes, its that each one requires a different tool to access and parse the data. A question as simple as “Did the malware execute after it was downloaded?” might require a combination of a dozen complicated and unmaintained open sources tools or a pricey commercial solution.
Original Price: $397
Our Price: $5
![5. Demo - [Linux] Interrogation of Compromised System - Mailserver](https://freeeducationweb.com/wp-content/uploads/2021/02/5.-Demo-Linux-Interrogation-of-Compromised-System-Mailserver.jpeg)



