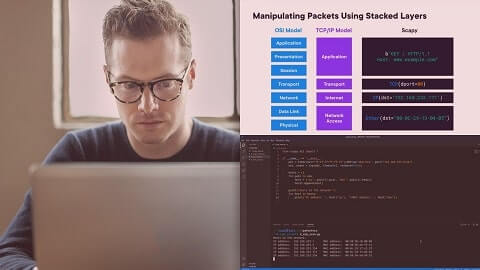
Offensive tools can trigger alerts, lead to early detection, and reveal TTPs and C2 infrastructure. In this course, Network Pen Testing with Python, you’ll learn to automate offensive security techniques with Python. First, you’ll explore Information Gathering and Initial Access. Next, you’ll discover how to conduct post-exploitation with Python. Finally, you’ll learn how to identify opportunities of exfiltrating data.. When you’re finished with this course, you’ll have the skills and knowledge of pen testing automation needed to assess the security controls of an organization.
HOMEPAGE – https://www.pluralsight.com/courses/python-network-pen-testing
Free Download Link-
Note: Comment below if you find the download link dead.



0 Comments