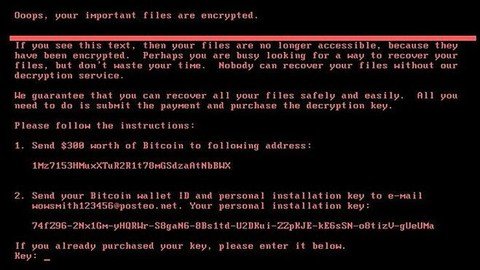
I had the initiative to create this course to teach a landing on what a real ransomware attack process looks like, using well-known tools used by notorious groups, let’s learn about the most famous groups,
accessing sites where stolen data is put for download by several different groups, let’s access forums famous for Russian hackers.
After the ransomware and notorious groups history steps, let’s go to the more practical step, learning how to create our python scripts, programming logic as an introduction and then, let’s start the file manipulation, moving on to AES, RSA encryption, etc. , these classes will help us create our ransomware
let’s learn to use tools that are used by these groups, a technique that is becoming very famous, called Living-off-the-Land for dazzling movement
and we are also going to create our own automated tools for mass data theft, ransomware, fake pages for sending emails to download malicious files, using as an example a page created by the North Korean APTs.
The course is still under development and that’s why new classes are added every week, classes are in English and there is also subtitles in case you have trouble understanding what I say.
The course is very practical, with windows commands, linux and many concepts in python, don’t wait for me to take your hand to guide you, there is Google for that.
Who this course is for:
- This course is intended for all those who want to learn the basics of the TTPs of a Ransomware attack.
What you’ll learn
- Python programming for file manipulation
- Cryptography
- About Ransomware and Notorious Groups
- Post exploration basics
- phishing
- Creating Symmetrical and Hybrid Ransomware
Free Download Link-
Note: Comment below if you find the download link dead.

0 Comments