Most enterprise networks today are managed using Windows Active Directory and it is imperative for a security professional to understand the threats to the Windows infrastructure.
Active Directory Pretesting is designed to provide security professionals to understand, analyze and practice threats and attacks in a modern Active Directory environment. The course is beginner friendly and comes with a walkthrough videos course and all documents with all the commands executed in the videos. The course is based on our years of experience of breaking Windows and AD environments and research.
When it comes to AD security, there is a large gap of knowledge which security professionals and administrators struggle to fill. Over the years, I have taken numerous world trainings on AD security and always found that there is a lack of quality material and specially, a lack of good walkthrough and explanation.
The course simulate real world attack and defense scenarios and we start with a non-admin user account in the domain and we work our way up to enterprise admin. The focus is on exploiting the variety of overlooked domain features and not just software vulnerabilities.
We cover topics like AD enumeration, tools to use, domain privilege escalation, domain persistence, Kerberos based attacks (Golden ticket, Silver ticket and more), ACL issues, SQL server trusts, and bypasses of defenses.
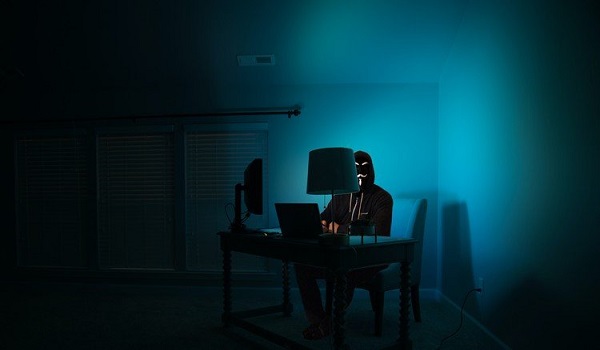
Attacking and Hacking Active Directory With Kali Linux Full Course – Read Team Hacking Pentesting
Who this course is for:
- Students who would love to become an Active Directory Pentesting Expert
- Students who would love to learn how to Attack Active Directory
- Students who would love a Job as a Red Team
What you’ll learn
- How to Use Metasploit to Exploit Active Directory
- How to Use Empire to Exploit Active Directory
- How to Use Evil-WinRM to Exploit Active Directory
- How to Use CrackMapExec to Exploit Active Directory
- How to Exploit Active Directory From Windows
- How to Do Active Directory Enumeration
- How to do Lateral Movement
- Active Directory Post Exploitation
- Active Directory Domain Privilege Escalation
- Active Directory Persistence Attacks
- How to use Kali Linux to hack Active Directory
- How to use nmap to Enumerate Servers
- How to exploit EternalBlue
HOMEPAGE – https://www.udemy.com/course/active-directory-pentesting-with-kali-linux-read-team-hacking/
Free Download Link-
Note: Comment below if you find the download link dead.



5 Comments
Smiley · May 11, 2021 at 8:39 pm
thankyou!
Smiley · October 19, 2022 at 6:57 am
dead link part 13,14,15
admin · October 22, 2022 at 2:09 am
Fixed.
kaiser · January 28, 2024 at 7:14 pm
Dude zippshare is dead. Can you handle this?
admin · February 10, 2024 at 9:27 pm
Link is fixed.