Description
Size: 19.3 GB
Who Should Attend FOR610?
FOR610 acts as a practical on-ramp into the world of malware analysis. It is useful both for individuals looking to enter this exciting field, as well as for those who seek to formalize and expand their skills in this area. Attendees who have found this course especially useful often have responsibilities in the areas of incident response, forensic investigation, information security, threat intelligence, and threat hunting. Course participants have included:
- Individuals who have dealt with incidents involving malware and wanted to learn how to understand key aspects of malicious programs.
- Technologists who have informally experimented with aspects of malware analysis prior to the course and were looking to formalize and expand their expertise in this area.
- Forensic investigators and security practitioners looking to expand their skillsets and learn how to play a pivotal role in the incident response process.
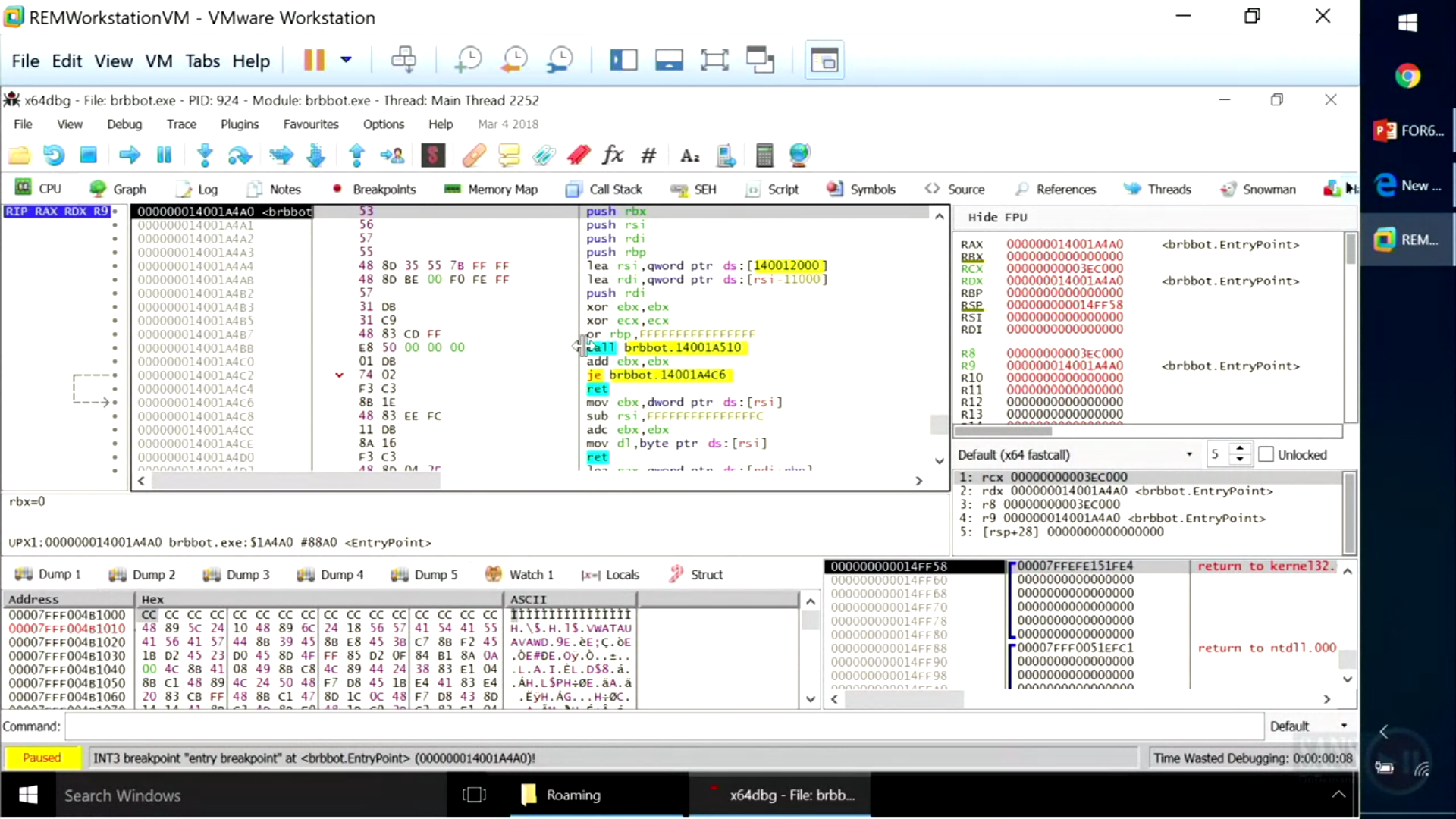
The course begins by covering malware analysis at an introductory level, then quickly progresses to discussing tools and techniques of intermediate complexity. Neither programming experience nor knowledge of assembly is required to benefit from the course. However, you should have a general idea about core programming concepts such as variables, loops, and functions, so you can quickly grasp the relevant concepts in this area. The course spends some time discussing essential aspects of the assembly language, allowing malware analysts to navigate through malicious executables using a disassembler and a debugger.