Description
Size: 912 MB
What is the target audience?
- Web Developers
- Web Application Pentesters
- Security Engineers
- Web Application Security Consultants
- Web Security Enthusiasts
- Hackers
- Students
- Web Application Designers
Curriculum
Section 1: Introduction
1.Node.js Security: Pentesting and Exploitation – Overview
2. Introduction to Node.js
Section 2: Node.js Security Issues
3. Global Namespace Pollution
4. HTTP Parameter Pollution (HPP)
5. Remote Code Execution with eval()
6. Remote OS Command Execution
7. Attacks due to Untrusted user input
8. Regex DoS
Section 3: Information Disclosure
9. Information Disclosure in Node.js Web Applications
Section 4: Secure Coding
10. Lack of Secure Code in Node.js
Section 5: Code Review
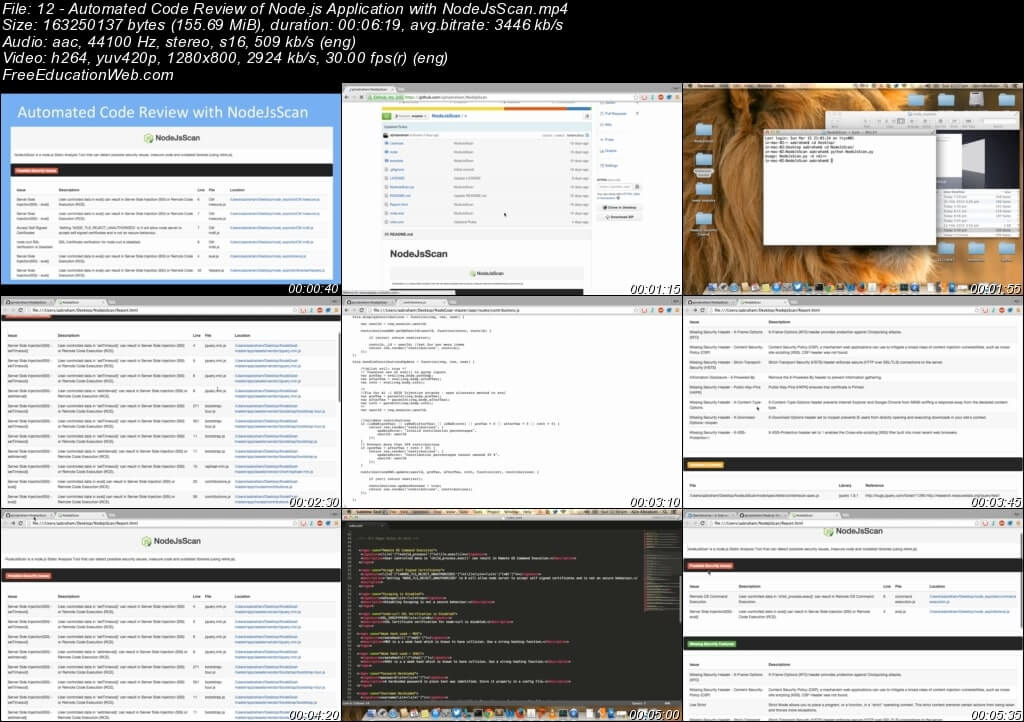
11. How to do Code Review of a Node.js Application
Section 6: Automated Code Review
12. Automated Code Review of Node.js Application with NodeJsScan
Section 7: Conclusion
13. Conclusion
14. Course Materials