Description
Size: 531 MB
Prerequisites:
Basic Computer Network knowledge – OSI and TCP/IP Model
Basic knowledge in common application and technology – Firewalls,DNS,IPS/IDS – HTTP/HTTPS
By the end of this course, students should be able to:
Identify key information on web server logs
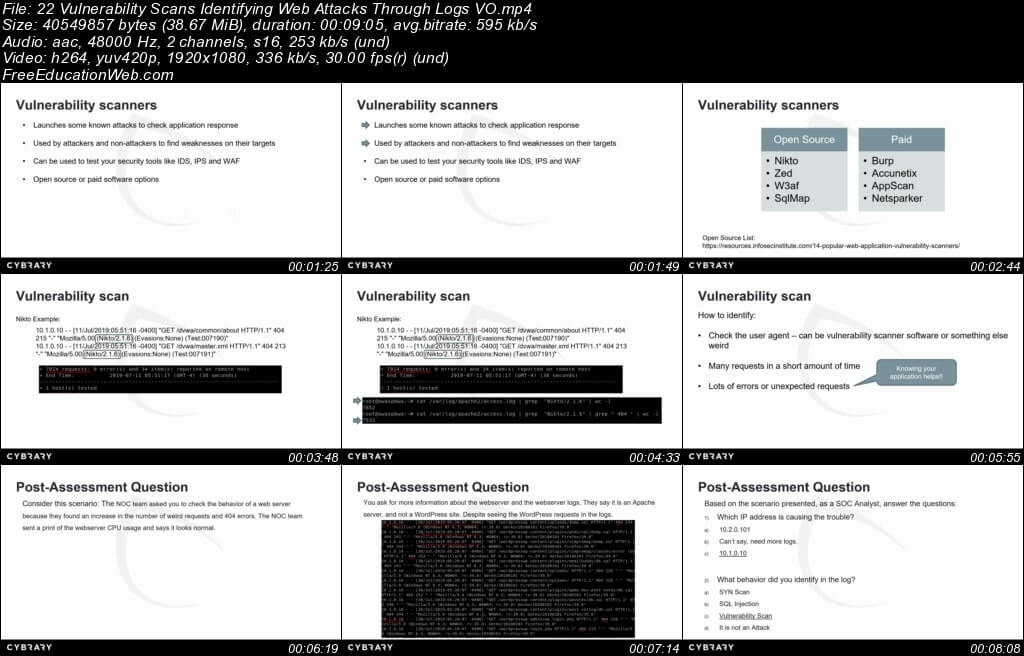
Identify malicious actions by analyzing logs
Identify web attacks after analyzing logs
In the Log Analysis training course, students will participate in a lab where they will learn to review different log files related to the Windows operating system. Students will learn to configure systems to log events, as well as to analyze system events.