Description
Size: 10.2 GB
What you’ll learn.
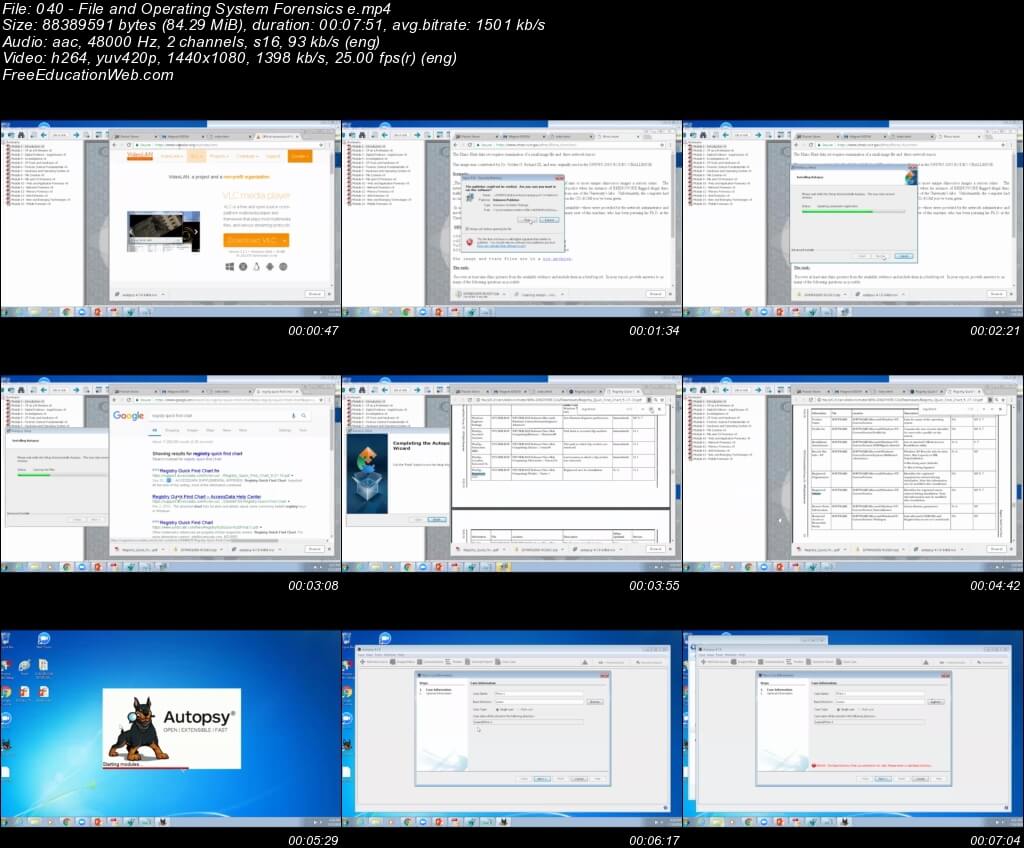
- Conducting forensics investigations
- Using popular forensics tools and techniques
- Gaining access to devices
- Discovering hidden data
- Legal issues around forensics
- And more!
Who is this for?
Basic computer skills, including the ability or desire to work outside the Windows GUI interface, are recommended. This skill path is designed for:
- IT and security professionals tasked with corporate forensics and incident handling
- Law enforcement professionals dealing with computer crimes
- Legal professionals
- Anyone with a desire to build their computer forensics skills!